Cybercrime has grown beyond just hacking files to asking for ransom before the files can be recovered. Most businesses have suffered losses from Ransomware encryption. The good news is that you can recover your files and not risk losing money, thanks to Ransomware decryption tools.
In this post, we’ll be taking a look at how to decrypt files encrypted by ransomware and some Ransomware decryption tools. Do well to read this post to the end because it’ll be very helpful.
Table of Contents
WHAT IS RANSOMWARE?

Ransomware is malware that is made to prevent a user or business from accessing files on a computer. Cyber attackers put businesses in a situation where paying the ransom is the quickest and least expensive option to recover access to their files by encrypting these files and requesting a ransom payment for the decryption key.
For increased motivation for ransomware victims to pay the ransom, several variants have included other capabilities like data stealing.
Ransomware is now the most apparent and prominent form of malware. Recent ransomware attacks have seriously hurt several enterprises, paralyzed public services in cities, and affected hospitals’ capacity to deliver essential services.
WHAT IS FILE ENCRYPTION?
File encryption is the use of complex algorithms to scramble or encode sensitive data and files. Once scrambled, the file becomes unintelligible and inaccessible to unauthorized persons but the effect only lasts for a short while. The encoding guards against hostile actors’ unauthorized access and alteration.
It prevents a file from being read by anyone besides the designated recipient or recipients. A useful option that enables you to make your sensitive data unreadable to everyone but the designated recipients is file encryption.
A key that the sender supplies is included with the encrypted data. This key, which enables decryption, typically takes the form of a password or passphrase, such as a string of alphanumeric characters.
You Might Like: Top 5 Frequently Asked Questions in Cybersecurity Interview
HOW DOES RANSOMWARE ENCRYPTION WORK?

The only difference between ransomware encryption and other types of encryption is that the ransomware gang controls the keys. The file’s bits will be taken by the encryption software, which will then scramble them using a cipher—a procedure that creates the encryption keys. These decryption keys can be used to unlock the file’s encryption and return it to its original usable state.
While some ransomware constructs its encryption tools that may only encrypt a portion of files to speed up the process, others employ industry-standard encryption or compression tools, such as 7zip and Winrar.
In either scenario, the encryption tool notifies the ransomware gang of the randomly produced encryption key. If the victim pays the ransom, the customer will receive the decryption tool and the random key needed to unlock the files.
Ransomware requires access to a target machine to encrypt the data inside and demand a ransom from the victim.
Although the specifics of implementation differ from one ransomware variation to another, they consistently follow the same fundamental three stages:
1. Infection And Distribution Vectors
Like all viruses, ransomware has a variety of ways to access a system within an organization. However, ransomware developers frequently favor a small number of distinct infection channels.
These include phishing emails. A malicious email may include a downloader-equipped attachment or a link to a website offering a malicious download. When a recipient of an email falls for a phishing scam, ransomware is downloaded and run on their computer.
2. Data Encryption
After gaining access to a machine, ransomware might start encrypting its files. This only requires accessing the files, encrypting them with an attacker-controlled key, and then replacing the originals with the encrypted copies because encryption technology is embedded into an operating system.
To maintain system stability, the majority of ransomware variations are selective in the files they choose to encrypt. To make recovery without the decryption key more challenging, certain variations will additionally take action to erase backup and shadow copies of files.
3. Ransom Demand
When file encryption is finished, the ransomware is ready to ask for payment. This is implemented in various ways by various ransomware versions, however, it is usual to have the display backdrop changed to a ransom note or to have text files added to each encrypted directory that contains the ransom note.
Access to the victim’s files is demanded in these notes in exchange for a specific sum of cryptocurrency.
In exchange for payment of the ransom, the owner of the ransomware will either give a copy of the symmetric encryption key itself or a copy of the private key that was used to protect it.
This data can be entered into a decryptor tool, which the cybercriminal will also supply, to utilize it to undo the encryption and regain access to the user’s files.
CAN ENCRYPTED FILES BE DECRYPTED
Yes! Encrypted files can be decrypted. But this depends on the type of encryption and access to the password to the file.
On Windows, you can use the Command Prompt, a command-line interpreter known as cmd.exe or cmd, to decrypt your encrypted files and folders.
This only works if you previously encrypted the file with the Cipher command and are running the same version of Windows and on the same PC. You cannot decrypt your data again if you are using a different computer or if Windows has recently been reinstalled.
If you used EFS to encrypt your file, decrypting it is very simple. Right-click the file and select properties. Under General, click Advanced. Then, untick the ‘Encrypt Contents To Secure Data Radio’ box and click on OK.
You’ll see another dialog box asking if you want to Apply changes to this folder or Apply changes to this folder, subfolders, and files. Choose whichever you want and select OK.
Your files will be decrypted in a few seconds. There are a lot of ways but these are some of the ways you can decrypt encrypted files.
You Might Also Like: How To Prevent Cyber Attacks (Top Secrets)
HOW TO IDENTIFY RANSOMWARE STRAIN AND ITS SIGNS
Determining how to decrypt files encrypted by ransomware requires knowing the precise strain of ransomware that has attacked a system.
IT administrators, CTOs, and developers can verify whether a known ransomware decryption solution is available for a certain situation in particular by identifying the strain.
The first step on how to identify ransomware strain is looking for ransomware signs, such as inaccessible data, sluggish or unresponsive machines, odd pop-ups or alarms, and the emergence of ransom demand messages. Once you’re certain that ransomware has invaded your machine, you must determine which precise malware strain it is.
Using automated tools to examine how the malware interacts with people and programs can also help to identify the specific ransomware strain.
As an illustration, behavior-based methods can be used to find ransomware signs like API requests and odd traffic. Once the ransomware strain has been discovered, it is crucial to find out if a decryption tool is known to exist for that specific strain.
It’s also crucial to keep in mind that some ransomware variants are made to remain invisible and might not have any known decryption tools. The only practical course of action in such circumstances is to follow the security measures we’ll give here.
HOW TO DECRYPT FILES ENCRYPTED BY RANSOMWARE
If you have been looking at how to decrypt files encrypted by ransomware, follow these steps:
Step 1: Identify the ransomware variant
Identifying the sort of ransomware that has attacked the system is the first step in retrieving files that have been encrypted by it. This can be accomplished by looking at the ransom message and file extensions of the malware.
The type of ransomware can be determined with the aid of a website like ID Ransomware. Sometimes, individual ransomware strains may have publicly accessible decryption tools.
Step 2: Backup encrypted files
It is crucial to back up files before attempting to decrypt them in case something goes wrong with the decryption procedure. It is advised to create a backup of the encrypted files and keep them in the cloud or on an external drive.
Step 3: Download a decryption tool
Download the decryption tool from a reliable source, such as the antivirus software maker’s website, if one is offered for the specific ransomware strain. Making sure the tool works with the specific ransomware strain is crucial.
Step 4: Run the decryption tool
To decrypt the files, download the decryption software and then follow the device’s on-screen instructions. Selecting the encrypted files, entering the decryption key, if one is given, or choosing a folder to save the decrypted files are some examples of how to do this.
The decryption procedure could fail if the incorrect settings or options are used, thus it’s crucial to carefully follow the instructions (hence the significance of creating a backup of any encrypted data before beginning this process).
Step 5: Check the decrypted files
Check the decrypted files to make sure they function properly when the decryption procedure is finished. Use an antivirus program to check the files to make sure there is no residual infection there. Additionally, store the decrypted files in a safe place.
Try a new decryption tool or contact a reputable data recovery agency if the files are still not operating properly.
Step 6: Remove the ransomware
The ransomware must be removed from the compromised system as soon as the data have been successfully decrypted to limit additional damage. Use antivirus software or adhere to other products’ directions to accomplish this.
You Might Also Like: Top Cyber security consulting firms making waves in the world
BEST RANSOMWARE DECRYPTION TOOLS
Another thing that’ll aid you in how to decrypt files encrypted by ransomware is the following Ransomware decryption tools.
1. Avast Ransomware Decryption Tools
30 free ransomware decryption tools are currently available from Avast for Windows operating systems. The following are some examples of ransomware variants:
- AES_NI
- Alcatraz Locker
- Babuk
- CrySiS
- CryptoMix (Offline)
- GandCrab
- Globe
- Jigsaw
- Troldesh / Shade
2. McAfee
McAfee’s Ransomware Recover (Mr2) is a framework created to reduce the time and resources needed by members of the cybersecurity community who have decryption keys and decryption logic to establish a decryption framework.
This tool can decrypt ransomware-encrypted user files, apps, databases, applets, and other files and objects. The excellent thing about this tool is that it is consistently updated when new decryption algorithms and keys become available to unlock files being held hostage by crooks.
3. Webroot SecureAnywhere AntiVirus
For the majority of Ransomware variations, this decryption tool works great. It starts at $23.99 per year and offers a 14-day free trial. Webroot is an antivirus program that scans swiftly and uses very little disk space. It removes all ransomware and unlocks data that have been encrypted.
4. AVG
AVG has a range of free ransomware decryption tools that can help decrypt ransomware-encrypted files. In addition, AVG’s endpoint security products (AVG Internet Security) have a ransomware protection capability.
By preventing file change, deletion, and encryption, this contributes to the protection of files on endpoint devices and helps avoid ransomware assaults.
AVG currently offers 7 free ransomware decryption tools, for the following variants:
- Apocalypse
- BadBlock
- Bart
- Crypt888
- Legion
- SZFLocker
- TeslaCrypt
5. Kaspersky Anti-ransomware Tools
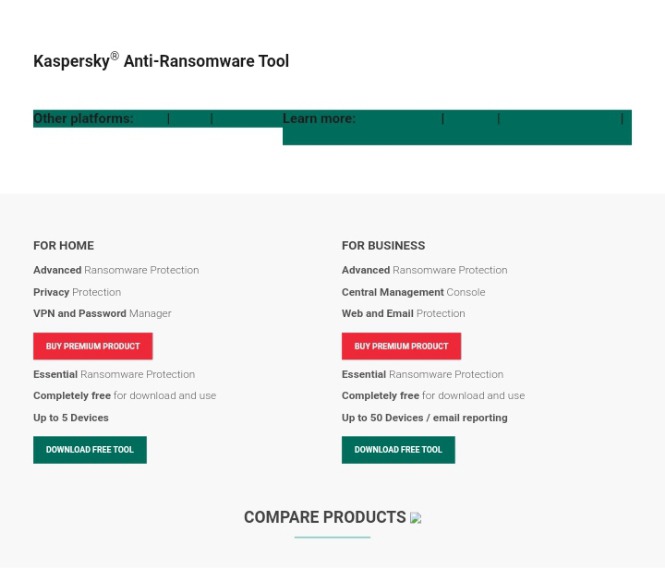
When ransomware strikes, you should turn to Kaspersky Anti-ransomware Tools. Specific strains of ransomware come and go, and some of them do so repeatedly. Sometimes Kaspersky is the first to identify a new ransomware infection and find it.
Kaspersky currently offers 6 free ransomware decryption tools, for the following variants:
- Shade Decryptor
- Rakhni Decryptor
- Rannoh Decryptor
- CoinVault Decryptor
- Wildfire Decryptor
- Xorist Decryptor
HOW TO PROTECT AGAINST RANSOMWARE
An effective plan can significantly reduce the cost and effects of a ransomware attack. Adopting the best practices listed below can lessen an organization’s vulnerability to ransomware and lessen its effects:
1. Regular Data Backups
According to the definition of ransomware, it is malware created so that decrypting encrypted data requires paying a ransom. A company can recover from an assault with little to no data loss and without having to pay a ransom thanks to automated, protected data backups.
A crucial procedure for preventing data loss and ensuring data recovery in the case of corruption or disk hardware failure is maintaining regular backups of data. Organizations can recover from ransomware attacks with the assistance of functional backups.
2. Patching
To guard against ransomware attacks, patching is essential since hackers frequently search the patches for the most recently discovered exploits before launching assaults on unpatched systems.
Because fewer possible vulnerabilities exist within the company for an attacker to exploit, firms must make sure all systems have the most recent updates applied to them.
3. Education and Training in Cyber Awareness:
Phishing emails are a common method for spreading ransomware. It is essential to educate people on how to recognize and prevent possible ransomware attacks.
User education is frequently seen as one of the most crucial defenses a company can employ, as many modern cyber-attacks begin with a targeted email that does not even contain malware but merely a socially-engineered message that tempts the user to click on a harmful link.
4. Install An Anti-ransomware Program
Because ransomware must encrypt each user’s files, it leaves a distinct fingerprint on each system it infects.
These fingerprints are used to identify anti-ransomware programs. Typical qualities of an effective anti-ransomware program include:
- detection of a large variety
- speedy detection
- Automatic recovery
- Restoration method not relying on frequently used built-in capabilities, such as “Shadow Copy,” which some ransomware strains target
FAQS
Can ransomware encryption be broken?
Yes. To remove the encryption imposed by ransomware, use decryption tools. Tools for decrypting files that have been encrypted by particular ransomware strains are known as ransomware decryption tools. These tools, which are often created by cybersecurity professionals, can be a useful way to retrieve encrypted files without having to pay a ransom.
Can encrypted data be decrypted by hackers?
Hackers can access the data by utilizing a variety of techniques to bypass encryption. Stealing the encryption key directly is the most popular technique. Another popular method is intercepting the data, either before the sender encrypts it or after the recipient decrypts it.
Can files that have been ransomware-encrypted be decrypted?
Yes, it is possible to decrypt ransomware-infected files. To combat the attack, a variety of ransomware decryption programs are available. The issue is that each ransomware variant requires a specific tool, and it is not always obvious which infection it is.
CONCLUSION
There is no assurance that files encrypted by ransomware will be successfully recovered or decrypted. Data that has been encrypted must be backed up, the type of ransomware must be determined, a reliable decryption tool must be downloaded, the instructions must be carefully followed, and the ransomware must be removed from the compromised system.
We hope our post on how to decrypt files encrypted by ransomware was helpful. Kindly drop a comment below to let us know your thoughts.
If you liked this article, then please subscribe to our YouTube Channel for videos relating to this article. You can also find us on Twitter and Facebook.
REFERENCE
- https://www.checkpoint.com
- https://blog.cubbit.io
- https://www.upguard.com
- https://www.comparitech.com
- https://www.esecurityplanet.com